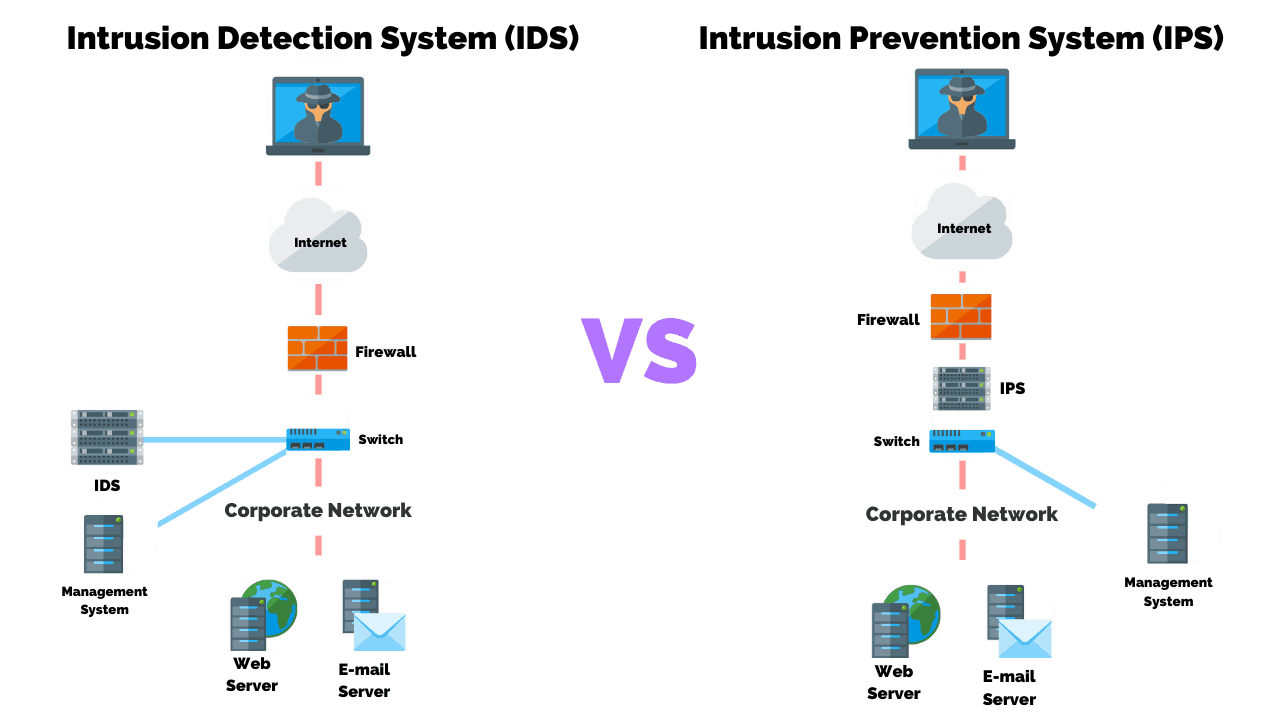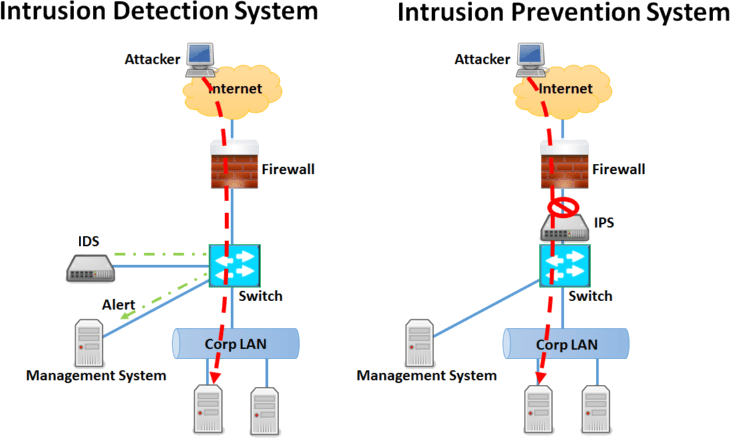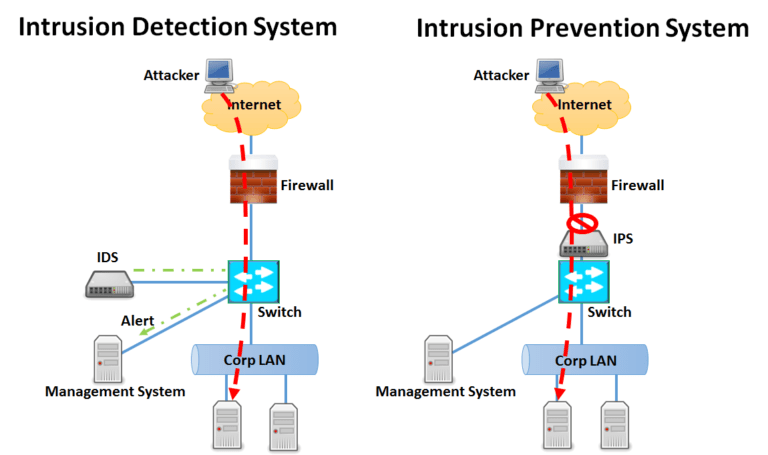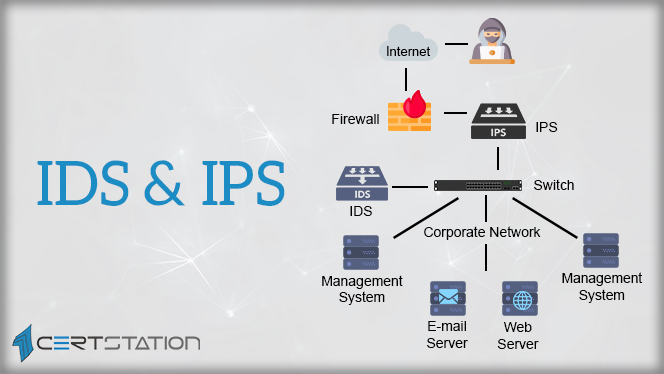
A Detailed Analysis of Intrusion Detection Systems and Intrusion Prevention Systems - CERTStation Blog
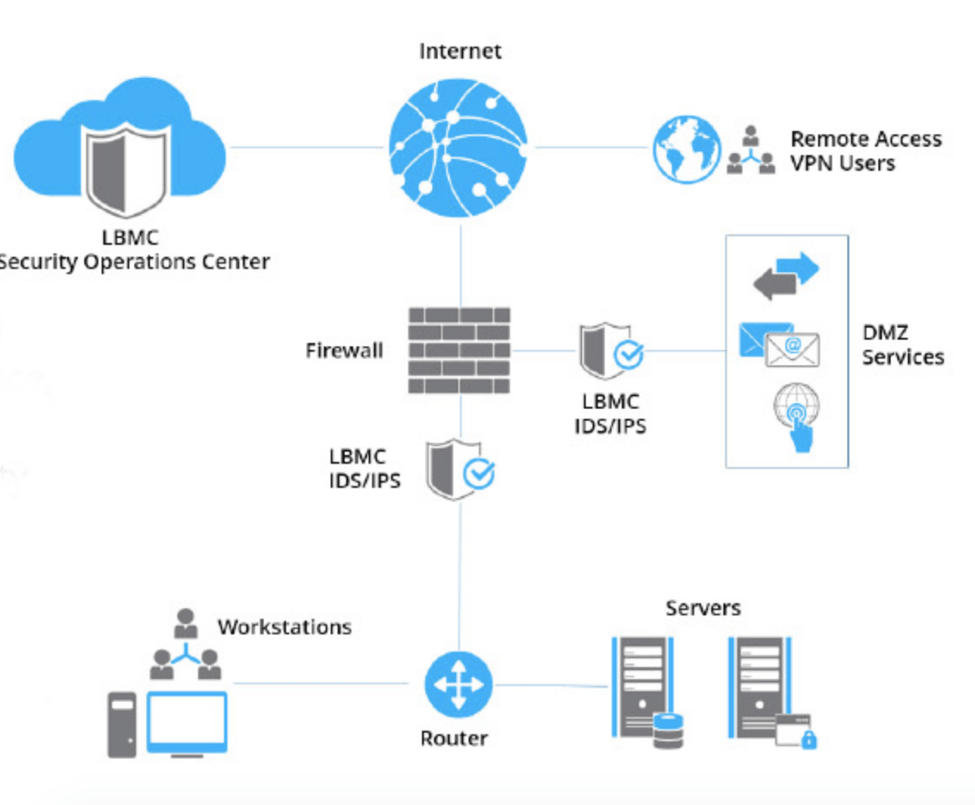
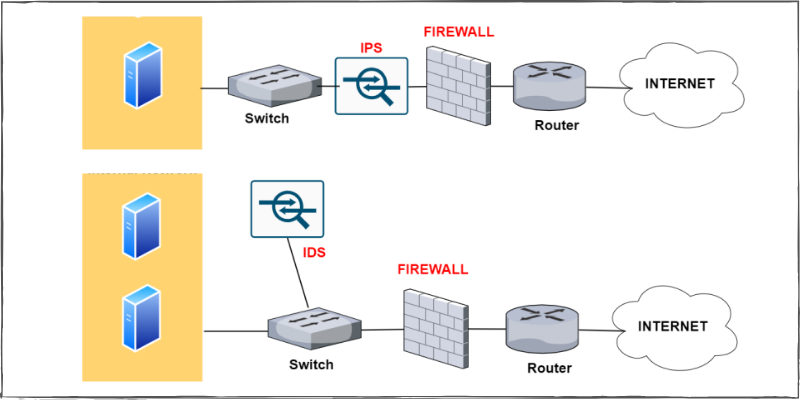
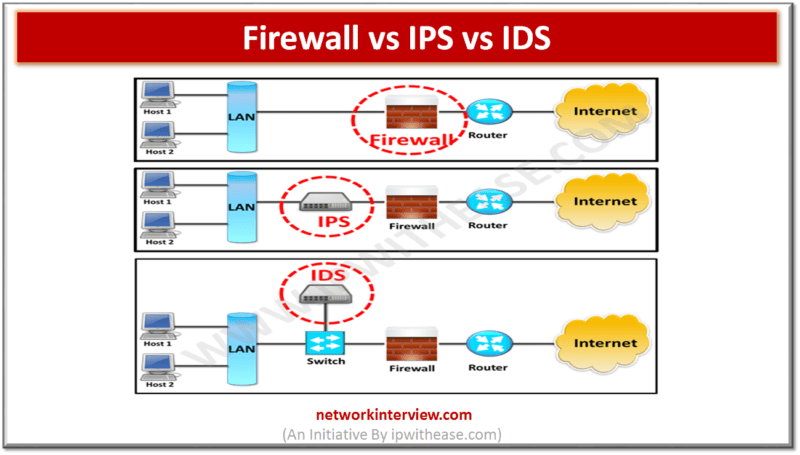
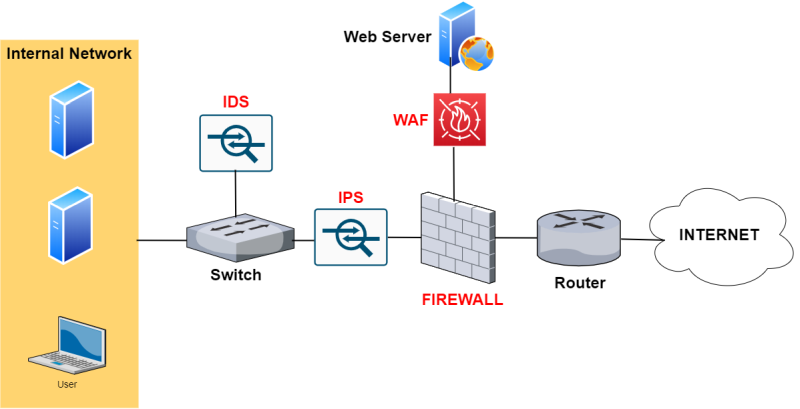
Introduction and difference between Security Firewall Vs IPS - Intrusion Prevention System Vs IDS - Intrusion Detection System - The Network DNA

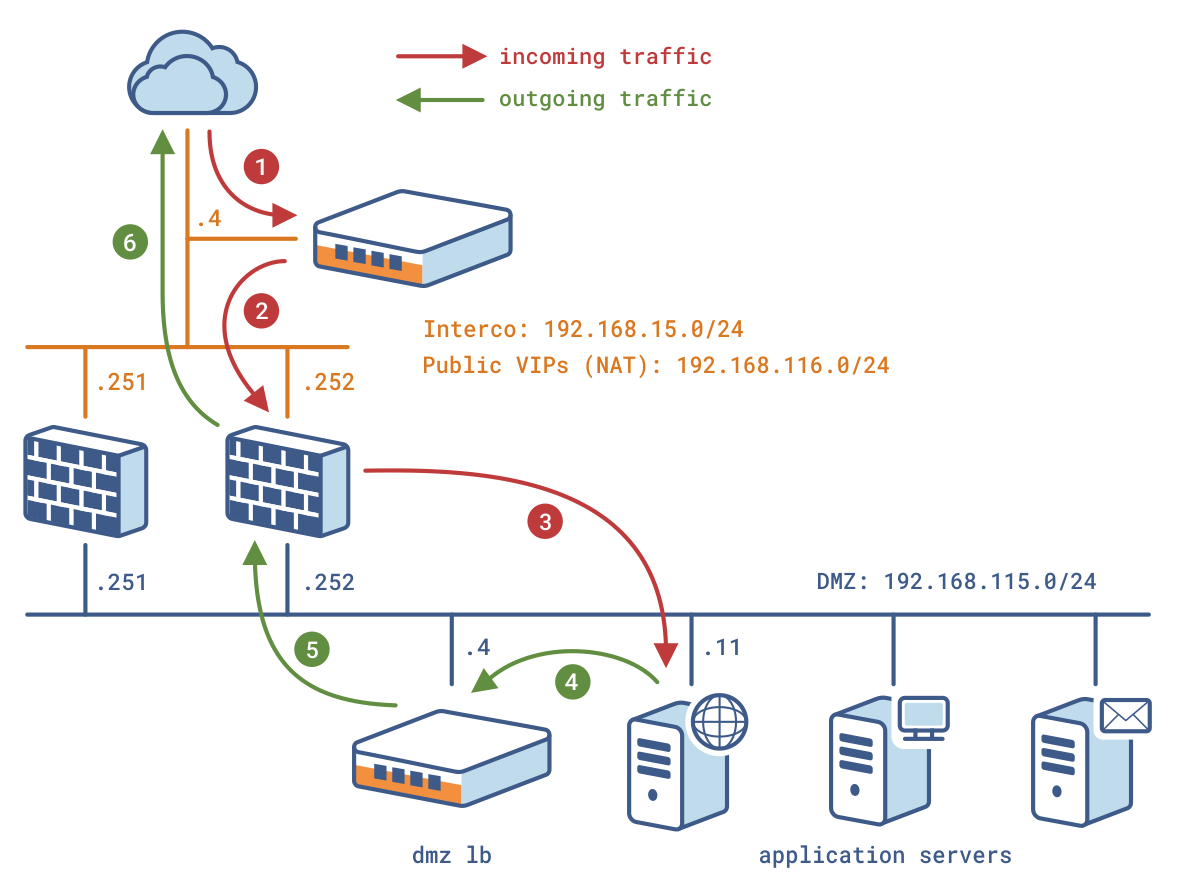
Comparison of network security tools- Firewall, Intrusion Detection System and Honeypot | Semantic Scholar

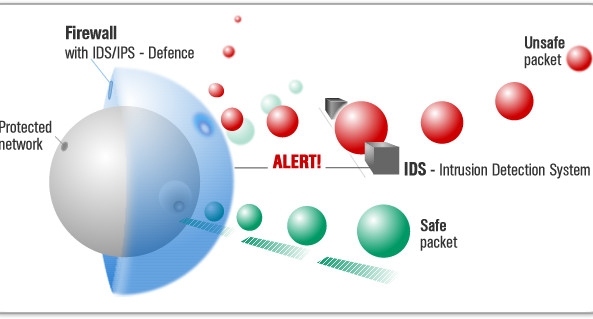
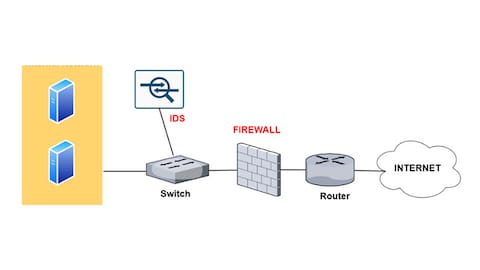
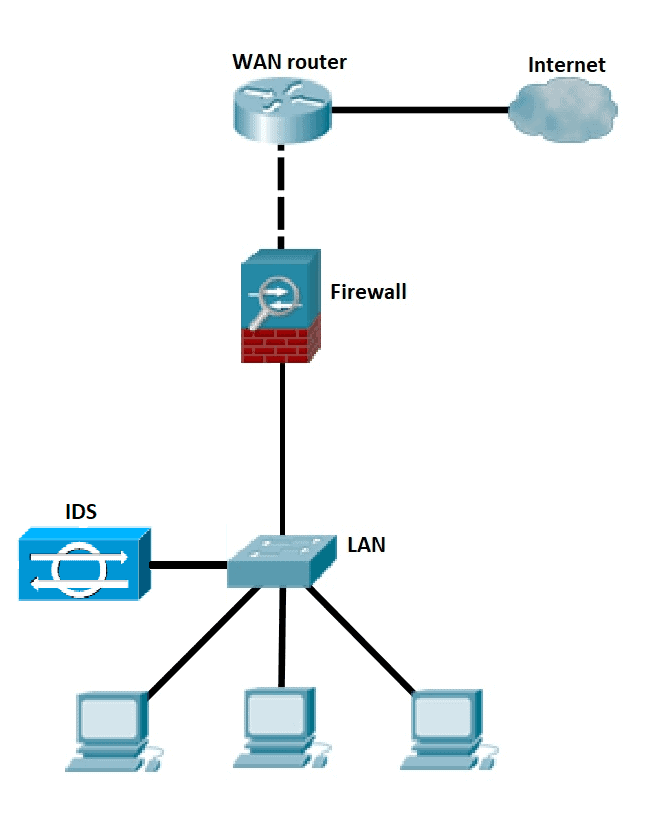
Defense Scenario II with firewall and the Intrusion Detection System (IDS). | Download Scientific Diagram

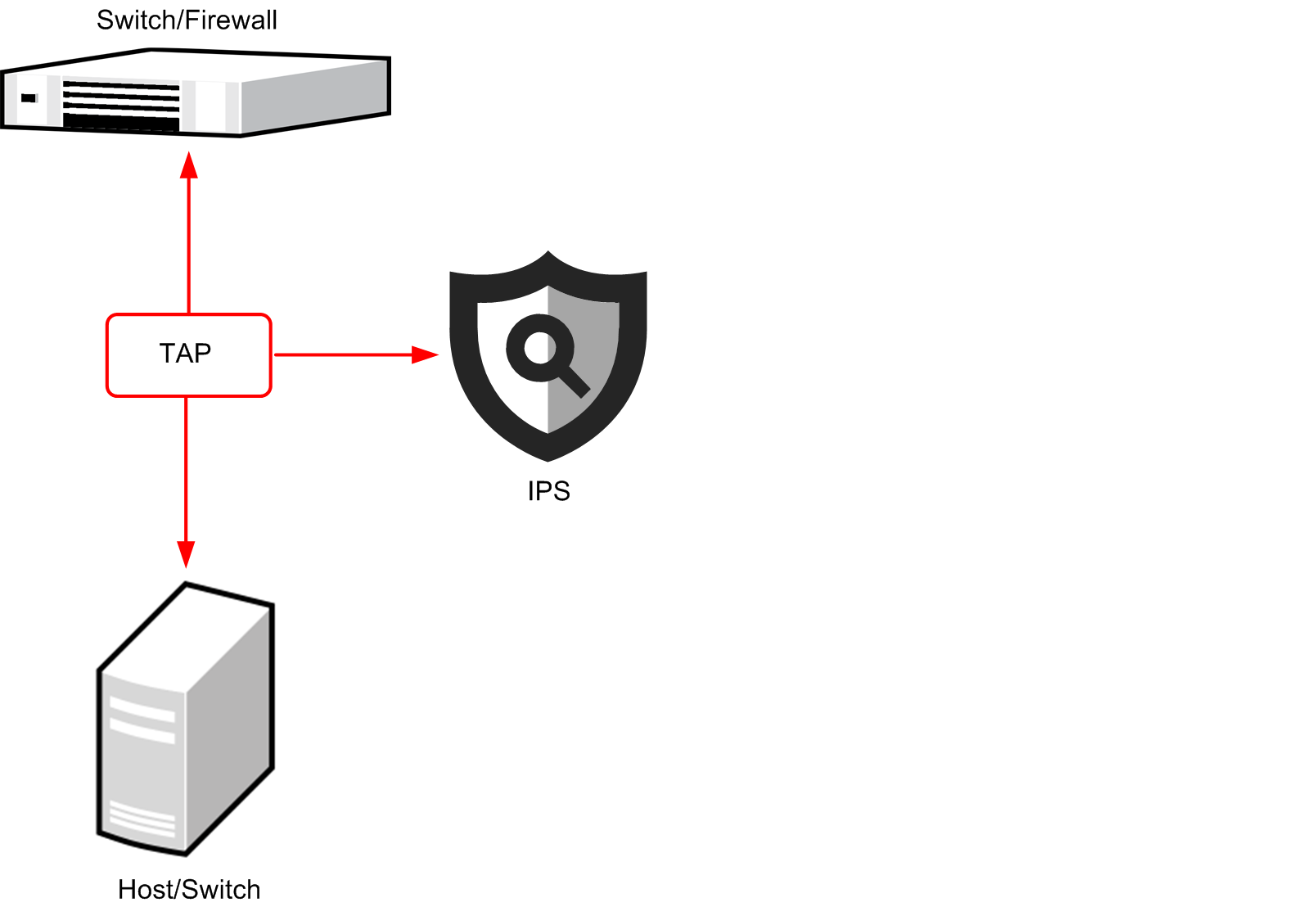
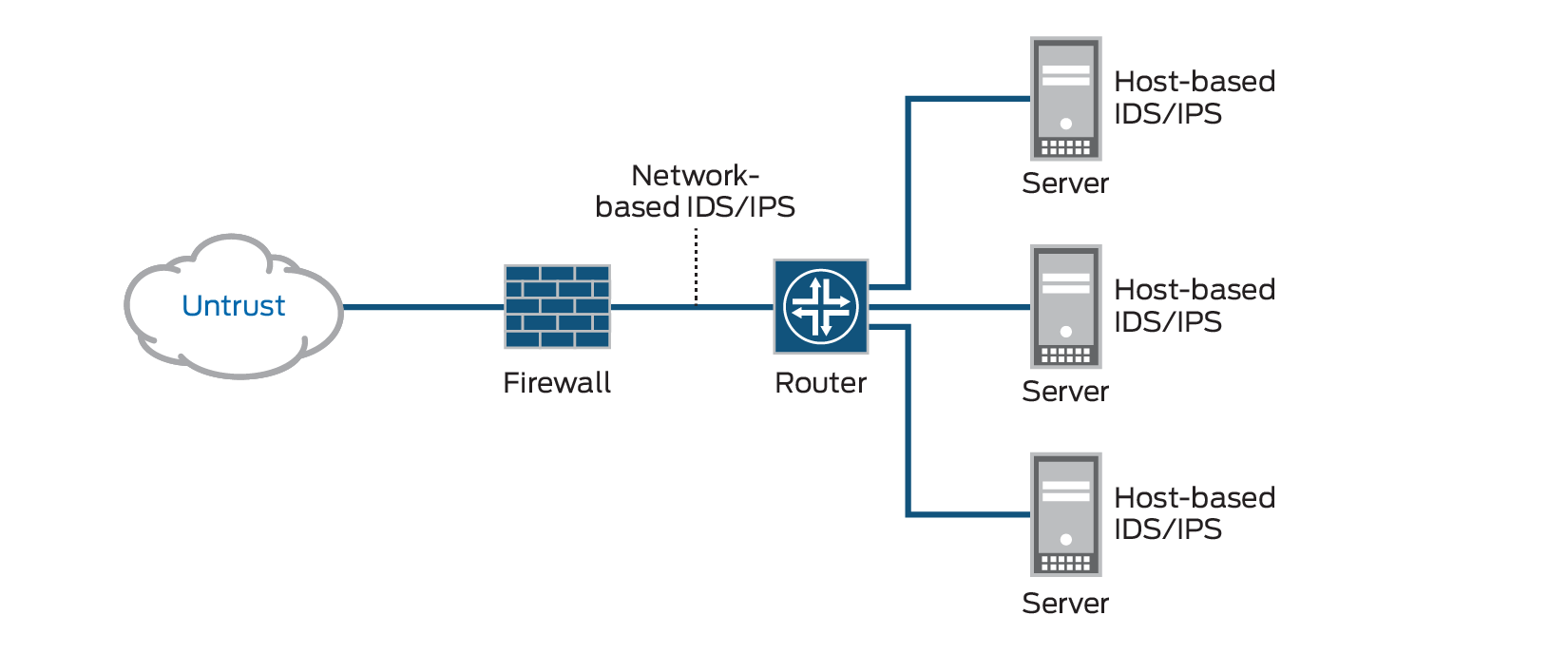
Intrusion Prevention System b. Preventing Attacks The IPS is located... | Download Scientific Diagram